Run Schedule Task on Windows
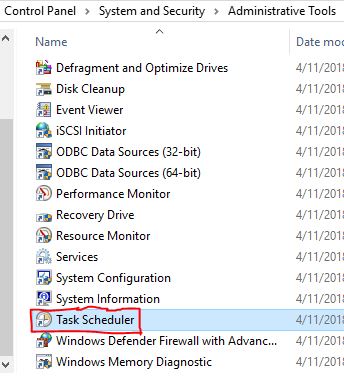
7 Steps to configuring your Schedule Task on Microsoft Windows This post will go over the steps to schedule a task on Windows. Microsoft Windows provides a Task Scheduler which can be configured to invoke or run a process, script or a task for a specified condition. The task can be specified to run at a particular time, Weekly, Daily, Monthly, or when user logs into the computer, boot up time etc. Tasks can be repeated or delayed as required. You can automate several tasks with the Windows Scheduler that can be run at a specified event or time. Follow each of the 7 steps below to configure your Scheduled Task. The screenshots with 7 steps are shown below are for creating a Task. The task is invoked at a particular time or when an event occurs. At the particular time or when the event occurs, the task is trigger by the Scheduler. Step 1: How to Access Task Scheduler To access the Task Scheduler, open the Control Panel, it is under Administrative Tools. Follow the path Contr