Web Services vs API
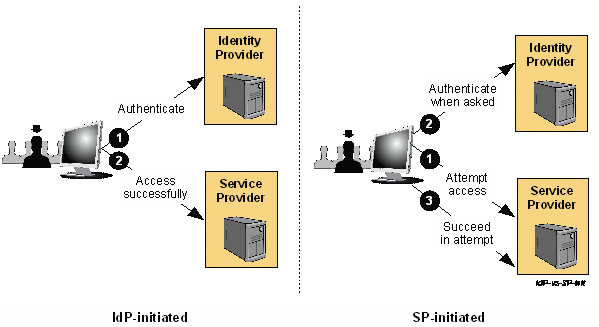
Difference between Web Service and API Both are means of communication. The difference is that web services communicate over network (http is the most common protocol used). API can use any means of communication. API is a generic term - here is video explaining what is an API . Whereas Web Service is a particular type of API. For example, an SOAP Web Service is a Web Service which is compliant with the W3C specification of a SOAP Web Service protocol/definition. So we can say: All Web Services are API but APIs are not Web Services. Web Services are API that uses web network for communication are web services